
PCI Compliance Levels: A Complete Guide
Do you know which PCI compliance level you fall into? Our complete guide tells you everything you need to know about PCI DSS.
Do you know which PCI compliance level you fall into? Our complete guide tells you everything you need to know about PCI DSS.
With the number of payment cards predicted to reach 31 billion globally by 20291, it's not surprising that cardholder data protection is getting a lot of attention. If your business handles cardholder data in any way, you need to know about PCI DSS compliance requirements.
What is PCI DSS?
The Payment Card Industry Data Security Standard (PCI DSS) is an array of security standards created in 2004 by the Payment Card Industry Security Standards Council (PCI SSC). The PCI SSC is composed of major credit card companies (MasterCard, Visa, American Express, JCB International, and Discover Financial Services).
The council was formed in order to enhance control over cardholder data and ultimately reduce card fraud.
What is PCI Compliance?
A company is considered PCI compliant if it follows PCI DSS requirements at all times, and can efficiently protect cardholder data by maintaining a proper level of security over cardholder data.
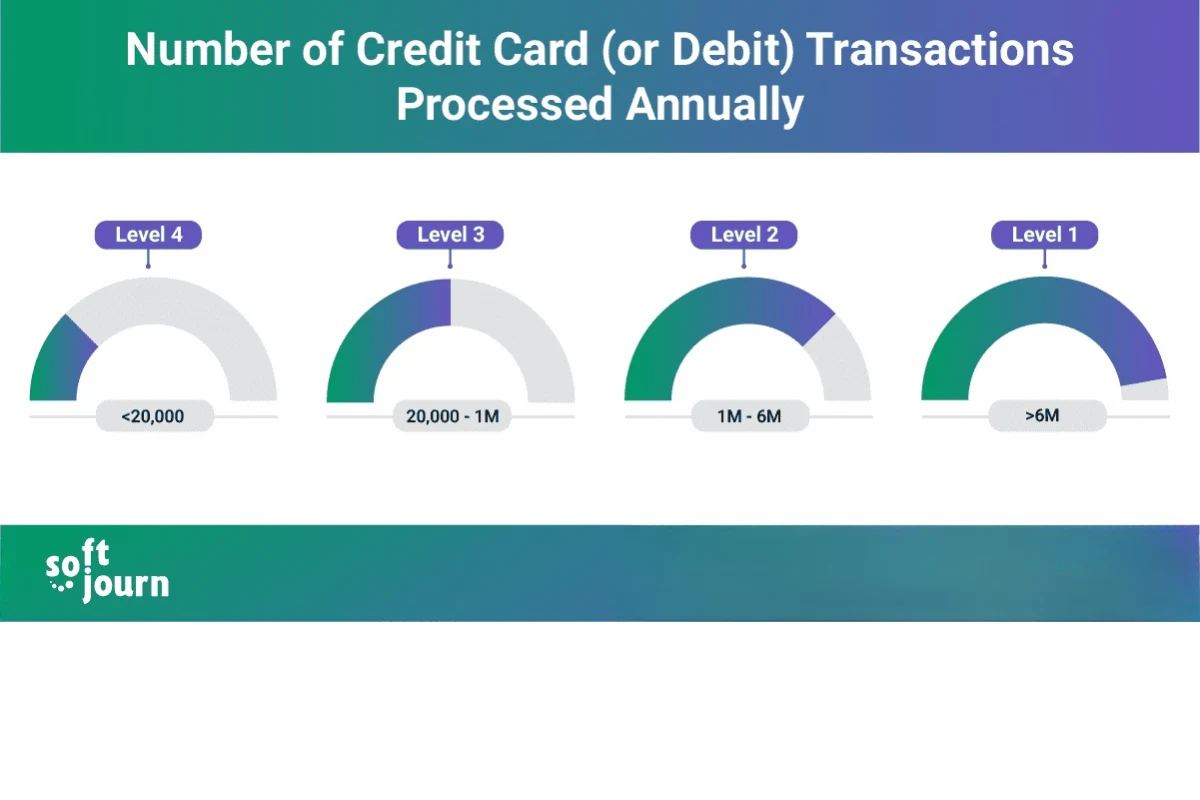
The level of PCI compliance and related validation requirements depend on a company's annual transaction volume.
The Benefits of PCI Compliance
A business that is PCI compliant assures customers that the security of their data and sensitive information is taken seriously. It's a sure way to build a long lasting relationship with clients.
Being PCI compliant also safeguards the company against malignant online scammers and fraud attempts.
The cost of being non-PCI compliant can be extremely high. It can seriously damage the reputation of the company, resulting in loss of customers, lawsuits, and fines from payment card issuers.
PCI Compliance Levels and Requirements Explained
PCI compliance is divided into four levels that are assigned depending on the annual number of card transactions of a company. Each level has its own criteria that a business must follow in order to remain compliant.
PCI Compliance Level 4 Criteria and Validation Requirements
Level 4 is considered the lowest level of compliance under PCI DSS. It applies to merchants who process fewer than 20,000 e-commerce transactions per year or up to one million Mastercard or Visa credit card transactions. These merchants shouldn't have encountered a data breach or attack which compromised cardholder data in any way.
Merchants who fall into this level can achieve PCI DSS compliance by meeting their acquiring bank's requirements.
Validation requirements:
- Completed Self-Assessment Questionnaire (SAQ)
- Quarterly network scans conducted by Approved Scanning Vendor (ASV)
PCI Compliance Level 3 Criteria and Validation Requirements
Level 3 applies to merchants who process between 20,000 and one million e-commerce transactions annually. It's important to mention that JCB International doesn't have Level 3. All merchants who process fewer than one million JCB International transactions per year are Level 2 merchants.
Validation requirements:
- Completed Self-Assessment Questionnaire (SAQ)
- Quarterly network scan conducted by an Approved Scan Vendor (ASV)
- Attestation of Compliance form
PCI Compliance Level 2 Criteria and Validation Requirements
Level 2 applies to merchants processing between one and six million credit or debit card transactions annually, fifty-thousand to two million sales using American Express, and fewer than one million JCB International credit card transactions.
Validation requirements:
- Completed Self-Assessment Questionnaire (SAQ)
- Quarterly network scan conducted by an Approved Scan Vendor (ASV)
- Attestation of Compliance form
- Additionally, a quarterly PCI scan may be required
PCI Compliance Level 1 Criteria and Validation Requirements
Level 1 applies to merchants who process more than six million credit or debit card transactions annually. It also applies to merchants who have suffered a data breach that resulted in the compromise of cardholder data or who has been identified as Level 1 by another card issuer.
Validation requirements:
- Annual Report on Compliance (ROC) by a Qualified Security Assessor (QSA) or Internal Security Assessor
- Quarterly network scan conducted by an Approved Scan Vendor (ASV)
- Submission of completed Attestation of Compliance form
PCI Compliance Levels and Requirements for Service Providers
Service providers usually assist merchants with the storage, processing, or transmission of cardholder data, which makes them beholden to PCI DSS. PCI compliance is also applicable for companies that provide services which control or could impact the security of cardholder data in some way.
Similar to merchants, service providers also have different compliance levels based on the number of transactions they perform per year. There are only two levels of PCI compliance for service providers.
Level 2 Service Provider Criteria and Validation Requirements
Level 2 concerns service providers that process less than 300,000 credit card transactions per year.
Validation requirements:
- Annual Self-Assessment Questionnaire (SAQ)
- Quarterly network scan by an Approved Scan Vendor (ASV)
- Penetration Test
- Internal Scan
- Attestation of Compliance (AOC) form
Level 1 Service Provider Criteria and Validation Requirements
Level 1 is for service providers that store, transmit, or process more than 300,000 credit card transactions annually.
Validation requirements:
- Annual Report on Compliance (ROC) by a Qualified Security Assessor (QSA)
- Quarterly network scan conducted by an Approved Scan Vendor (ASV)
- Penetration Test
- Internal Scan
- Attestation of Compliance (AOC) Form
Achieving level 1 compliance enables the business to appear on Visa's Global Registry of Approved Service Providers.
Self-Assessment Questionnaire For Your Compliance Level
Companies with PCI compliance levels 2 to 4 can complete a Self-Assessment Questionnaire (SAQ) instead of having an external audit2. There are various SAQs available to meet different merchant environments and it's very important for companies to choose the right one as they are based on the ways the payment card information is processed.
SAQs consist of a series of yes-or-no questions for each applicable PCI compliance requirement. If you answer no to a question, your company may be required to add future remediation dates and associated actions.
If you are not sure which SAQ to use, ask your acquiring bank or payment card brand for help. When a business assesses itself using the wrong set of requirements, they waste time, effort, and resources to meet objectives that are not applicable.
12 PCI DSS Requirements
PCI SSC outlines 12 requirements that every business must reach to become PCI DSS compliant. Each requirement is also divided into sub-requirements, which can be difficult for smaller companies to comply with if they do not have the assistance of an expert.

New Challenges and PCI Compliance Standard Update in 2022
With the rise of e-commerce - especially since the pandemic - online payments have grown enormously, and this has led to a great increase in credit card fraud. Individuals and small companies are especially easy prey for hackers, and it falls to credit card security standards to properly respond to the surge in fraud levels.
The current PCI 3.2.1 standard was an up-to-date solution in 2021, but the Security Council has recently decided to update the standard to PCI DSS v4.0. The changes the update will make to the PCI Security Standard are significant, because compliance will now be seen as a constantly evolving process. This dynamic standard ultimately aims to secure payments better than ever before.
After two years of development, the expected time to finish v4.0 is sometime between late 2024 and early 2025. The latest version is now open for comments, and is has become clear from the amount of comments garnered that the new standard is attracting a lot of attention.
Here are those that attracted most attention:
- Cryptographic protection of transmitted cardholder data (CHD).
- Strict access authentication and user identification. Specific requirements concern: stronger passwords and two-factor authentication, access history logs, and frequency changes.
- Restriction of physical access to sensible data.
- Testing of security systems and processes.
- Implementation of adequate security programs and policies.
Main Points of the Update
The main objectives of the PCI DSS compliance v4.0 update focus on several different aspects.
Mitigate newly emerging risks regarding cardholder data. The new standard will aim to increase the number of testing points so more data will be needed for validation and other procedures to achieve security measures.
Enhance flexibility for member companies to implement controls. The new standard will add more flexibility and support for a variety of methodologies. Payment industry players will be able to enforce changes without jeopardizing the safety of their clients data.
Enact new routines regarding security. Multi-factor authentication will likely adopt NIST password guidance, which would lead to the creation of safer and stronger passwords. 3D Secure protocols will also provide a greater layer of authentication. Encryption standards will be tested more frequently to ensure the quality is high.
Generally, the PCI council provided these key recommendations for the upgrade:
- Further reduction of sensitive cardholder data exposure
- Usage of stronger passwords
- Timely updates
- Better encryption technology
- Payment partners must be carefully chosen
- The change of authentication requirements
How Softjourn Helps Clients Attain PCI Compliance
While Softjourn cannot assist with the PCI DSS audit itself, we can help make your system secure and compliant. We have done so for many clients in the past, including a prepaid card company that has issued 10 million cards over its lifetime. We can help you prepare, including reviewing code and processes that will be examined during an audit. After the audit has taken place, we work with our clients to assist them in any necessary corrections. We follow PCI and Payment Application Data Security Standard (PA-DSS) guidelines in the development of payment data security software to ensure your successful certification from compliance services vendors.
Achieving PCI DSS compliance means that a business has taken all necessary steps to protect its clients and their sensitive data. Some of the biggest benefits of ensuring the compliance of your company are more secure transactions, better data management, and meeting global standards with multiple layers of security for safe transactions. Other benefits of PCI compliance include:
- Showing users they can trust a company to protect their data
- Helping prevent security breaches and theft of payment data
- Improving a company's infrastructure in terms of efficiency and security
Many of our clients have recognized the importance of PCI compliance checks and utilized their partnership with Softjourn to ensure their application is ready for a compliance audit. With our considerable experience in payments and ticketing, Softjourn's team of experts is able to successfully solve existing issues and upgrade our clients' applications.
Case Study: Updating Security Measures to Achieve PCI Compliance
A US-based company, focused on workforce spend management, came to us with a need to improve their security protocols. The goal of the project was for Softjourn to implement a multi-step process for upgrading the client's software.
First, we reviewed their current security build and identified weaknesses and potential vulnerabilities. This allowed us to evaluate what solution would work best for our client and provide them advice when deciding how they wanted to proceed.
Once the security schema was in place and upgrades were tested to ensure they met the desired outcome, we applied new metrics by which to test the security upgrades. This would allow for proactivity in anticipating any future security issues. We also integrated a log analytics tool to review attempted logins and identify potential attempted hacks.
We implemented both fingerprint and facial recognition biometrics for our client's mobile application on Android and iOS as an additional method of authentication to help them prevent unauthorized individuals from gaining access to critical assets. Through our collaboration with this client, we were able to help our client update their security measures sufficiently enough that they achieved PCI compliance.
Case Study: Improving Security Paves the Way to PCI Compliance
A Canadian-based client was worried about their level of PCI compliance, so they reached out to Softjourn for assistance. They were looking for a reliable partner to help them continue offering services with the same level of quality, but with improved security. Our project had three major goals:
- Design solutions to improve security
- Develop existing products
- Research what is needed to support further improvements
Softjourn's team worked directly with the client's Solutions Architect. Our team's first step was to become familiar with the client's system to ensure our recommendations would be aligned with their tech stack.
The next, and more complex part of the project was developing dashboards for monitoring the application system. Implementing dashboards requires additional knowledge, so the team needed some time to analyze the client's system and better understand its structure. Finally, Softjourn's experts created a list of recommendations in order to improve the security of our client's system, while maintaining their existing products.
Through Softjourn's guidance, our client recognized how important it is to keep their systems up to date to protect their customers from identity theft and fraud. Maintaining a consistent and ongoing security process, by remaining vigilant about new fraud techniques and educating employees about them, helped the client establish a well-rounded fraud prevention process, which is essential for reaching PCI compliance.
Case Study: Preventing Fraud with PCI DSS Compliance
Regulated standards are one helpful way for companies to know if they are doing everything they can to prevent fraud. Where the medical and education industries have HIPAA and FERPA to regulate privacy and security, the financial industry has the Payment Card Industry Data Security Standard (PCI DSS).
The Background
Prepaid debit cards are on the rise; as of 2016, users spent about $100 billion4 with the easy-to-use payment method. More Americans are turning to prepaid cards as a method of curtailing spending and staying out of debt. Prepaid cards are essentially debit cards without a bank account, which protects the spender from overdraft fees; they're also unlike credit cards since they only have what the spender puts on them and don't involve interest rates.
One of Softjourn's clients uses these cards to help their customers monitor employee spending by providing a transparent, efficient, and scalable solution for expense control. Of course, as with any company that operates in the digital marketplace, our client is heavily invested in securing their customer's information. Not only for their own reputation, but to protect their clients against identity theft and fraud that can plague victims for years.
They turned to us for help when it came to abiding by PCI DSS standards, one of the most effective ways to prevent fraud before it happens.
The Need
Unlike HIPAA and FERPA, PCI DSS isn't a government mandate. It was conceived by the five major credit card brands in 2004 in an attempt to create a cohesive understanding about fraud prevention for all merchants. The PCI Security Standards Council (PCI SSC), a separate group made up of members from the five brands to monitor the standards, have since updated the DSS as new technology and needs arise.
The PCI DSS covers six goals and 12 associated requirements5 that all merchants must abide by; the guidelines are broadly written to allow for a number of different implementations depending on a business's software security lifecycle. The PCI SSC provides a further breakdown and an additional 200 sub-requirements to provide suggestions on achieving each of the goals.
Merchants found in noncompliance after experiencing a security breach receive fines from $5,000 to $10,000 a month6 until they can demonstrate compliance. This is in addition to other damages merchants must deal with when responding to a data breach, including lawsuits, inherent financial losses, and a blow to their customer base. Moreover, maintaining PCI DSS compliance is clearly one of the best ways a merchant can prevent fraud—a 2010 Verizon study found that 79%7 of breached retailers were noncompliant.
The Solution
Softjourn implemented a multi-step process when upgrading the security of our client's software. What should be noted first is our client seeking out a third-party vendor for their software upgrade; a tenet of DSS is ensuring that all team members involved in designing and implementing a security solution be aware of the standards related to their particular role. Softjourn's technical expertise and acumen made them a clear choice of business partner in ensuring the security and privacy of our client's customers.
Next, we reviewed the current security build and identified weaknesses and potential vulnerabilities. This allowed us to evaluate solutions and provide our client with expert advice when deciding how they wanted to proceed. Once decisions were made, we developed a high-level roadmap that our client reviewed and approved before any work started. This roadmap would ensure that all involved in the project were aware of the changes, and that no part of the upgrade process would delay and potentially create issues that could not only increase the cost for our client, but could also possibly create new vulnerabilities in the future.
Once the security schema was in place and upgrades tested to ensure they met the desired outcome (for example, identify vulnerabilities and prevent attacks, etc.), we implemented new metrics by which to test the security upgrades and remain proactive in anticipating potential security issues before they happened. This included integrating a log analytics tool to review attempted logins and identify potential attempted hacks.
We also implemented both fingerprint and facial recognition biometrics for our client's mobile application on Android and iOS as an additional method of authentication to help prevent unauthorized individuals from gaining access to critical assets.
Conclusion
Keeping your company's systems up to date is one way to ensure you're protecting your customers from identity theft and fraud. Maintaining a consistent and ongoing security process that also involves educating employees and remaining vigilant regarding new fraud techniques and new technologies will help create a well-rounded fraud prevention process that can help your company now and in the future.
Softjourn is more than happy to provide assistance when it comes to adhering to PCI DSS standards. Reach out today to discuss your needs and how we can help!
Final Word
We can also assist in completing a relevant SAQ for your company. While being a third-party technology provider, we help our clients clearly understand the PCI requirements that are applicable to them. This avoids wasting time and money associated with filling out the wrong assessment. We support management, departments, and technical experts with our experience in PCI projects within acquirers and issuers.








